Security and Privacy Guidance Blog - Updated Regularly
Last Updated February 2025
Security and Privacy: Whether you're at home, work, or elsewhere, Network Security and Privacy aims to protect your network, devices, software, accounts, and personal data from unauthorized access. This type of access can occur through user behavior exploits (phishing or malicious websites), malware, vulnerabilities in software and devices, misconfigurations, or third-party breaches.
A compromise of your personal and financial information could lead to identity theft - and the loss of your money, your good credit rating, and your overall financial health.
If you are a victim of a scam or fraud, you can file a complaint with the Federal Trade Commission at https://ReportFraud.ftc.gov and the FBI’s Internet Crime Complaint Center at https://ic3.gov
Key Security Concepts drive the information on this page.
Using a password manager with 2-factor authentication helps insure against reused passwords (and credential stuffing attacks), as well as compromised password access via a stolen password or phishing website password disclosure.
Always using an trusted path (bookmark and verify url) to access important accounts goes hand in hand with not clicking links.
Configuring for Security and Privacy provides a foundation to help protect yourself WHEN you are exposed to a malicious actor attack.
Home Network Structure
Gateway is a boundary system that separates different security domains; here, it defines your Home Network through the WiFi definition
Gateway device (blue box) may be provided by Verizon or Comcast or purchased by homeowner
WiFi is defined by frequency (like a TV channel = green/red areas) and also by VLAN (a “tag” red/pink operate on same frequency (red) but are still separated (Main WiFi and IoT WiFi))
Some devices only work on one frequency (for example, the Green IoT 2.4 GHz Network); others can move automatically or may be assigned to only one frequency. Devices connect to Home Network through WiFi (no wire) or wired (physically connects device to the router or modem with a cable)
WiFi is like a voice - it needs to be heard to be useful; Gateway in home placement helps, and segregation provides useful isolation. Minimum support should be WiFi 6 (5e, 7 or 8) for WPA3 encryption
Bucks County Home Networks Services focus on the Gateway (Router/Cable Modem), Home WiFi, Computer, Mobile Phone and User Account Settings**
** With 25 years of direct experience with cable architecture and with all of the largest cable and telco operators in the United States, Bucks County Home Networks can also help with TV, Cable, or Streaming Services Device configurations as well (which may reduce monthly cost, help with home network set-up, or channel/service navigation).
Security and Privacy Guidance
The Guidance is provided as a public service. It is intended to provide reasonable actions to consider; it is not intended to be bulletproof in terms of home security or privacy - much depends on the underlying devices and software as well as individual behavior and the evolving nature of security and privacy risks. Although this Guidance is reviewed and updated regularly, readers are advised that any statement on security may quickly become out of date.
Problem: Security and Privacy - Defense can be both Tedious and Difficult to Navigate
Solution: Education, Best Practices, Cyber Hygiene and User Behaviors are the Strategy
Goal: Always practice a Secure Mindset every time you go online or use your devices
The Guidance on this page leverages the three most important principles of cybersecurity - Zero Trust, Least Privilege, and Defense in Depth which assume that the integrity of the network and credentials may already be compromised. Meaning and practice: resource access requires strong identity verification every time it is requested (Zero Trust) and should be restricted in both actual access rights and time that access is allowed (Least Privilege). Multiple layers of different security technology (Defense in Depth) provide better protection than a single layer.
Education, Best Practices, Cyber Hygiene and User Behaviors are the Strategy
Computer/Phone are on either Main WiFi Networks; IoT devices are split on IoT WiFi’s
Improve your home network security and privacy posture
Background: You should assume that Personally Identifiable Information (PII) including your name, date of birth and social security number, is available online and may be utilized to steal your identity or your money. As cyberattacks become more sophisticated and Artificial Intelligence (AI) makes attacks easier, individuals must stay informed, practice good security habits, and use available product features to help protect themselves, their devices, and their loved ones. Some of the most significant cybersecurity threats can be thwarted with user behaviors and protections available in the devices you already have, but that you do not currently use.
As Product Security and Privacy controls evolve such as vulnerability updates or improved encryption algorithms, associated configurations should be updated when available. Your home network, computer and mobile devices are the most sensitive and critical devices, as they contain personal information like banking details, credit cards, contacts, taxes, documents, and photos. These devices often have layers of configuration that require special attention to security and privacy.
Trust and Advice: The National Security Agency (NSA) and Cybersecurity & Infrastructure Security Agency (CISA) have useful best practices guides and information for your home network. The FBI has a useful page on Credit/Debit/EBT Card Skimming. These links are provided for self-education and convenience. Always verify a link is what you expect - in this case, specifically including the “https://” indicates a secure link protocol is being used and “.gov” indicates a U.S. government domain - as well as carefully looking at the rest of the link.
NSA link on Home Networks Best Practices (February 2023).
NSA’s Mobile Device Best Practices (September 2021; despite the age, it is still applicable).
CISA guidance on Mobile Communications Best Practices (December 2024)
https://www.cisa.gov/sites/default/files/2024-12/guidance-mobile-communications-best-practices.pdf
FBI webpage on Avoiding Credit / Debit / EBT Card Skimming
https://www.fbi.gov/how-we-can-help-you/scams-and-safety/common-frauds-and-scams/skimming
CISA put together education modules on cybersecurity for “high-risk communities” (journalists, human rights defenders, and others who are at higher risk from cyber threat actors because of their identity or work), but CISA also notes that “this guidance will benefit any individual seeking to improve their personal cybersecurity posture.”
https://www.cisa.gov/audiences/high-risk-communities/projectupskill (this is a deep dive set of education modules)
1. Control Your Online Identities and Information
Restricting Access: Freeze Your Credit and Review Periodically Strongly recommend freezing your credit through all three credit bureaus to protect against someone using information about you to potentially create fraudulent transactions or open a line of credit in your name. There is Zero Trust for unknown entities potentially checking your credit with your personal information (name, date of birth, social security number) and Least Privilege for opening anything (deny access if they try).
In the future, you will need to temporarily unfreeze the credit when applying for anything requiring a credit check such as a new credit card or loan - this inconvenience is well worth the effort). For initially creating your individual SSA user account, unfreeze Experian (SSA used this service for identity verification at the time this guidance was captured) while - then refreeze after the account is created.
Access your credit report, check your credit score, place fraud alerts, and learn more about protecting your credit on Credit Bureau Sites. Review monthly or quarterly for unexpected activity or changes.You will need to contact each bureau individually online, by phone or by mail (instructions are available on each site):
Equifax: https://www.equifax.com
Experian: https://www.experian.com
TransUnion: https://www.transunion.com
NOTES: Your home internet setup depends on both your Internet Service Provider (ISP) (such as Comcast, or Verizon FIOS) and the gateway (either provided by the ISP or purchased separately). The gateway (which could be a router, cable modem, or mesh system) is a demarcation point between your home network and the internet. If you want to compare Internet Service Providers to potentially save money on your monthly internet bill, https://www.whistleout.com/Internet/United-States is a one site to check - typically, the lowest speed plan in Bucks and Montgomery Counties is more than sufficient for most people. Any performance problems will very likely not be related to, nor improve, with a faster speed from your ISP.
Home Networks: Your sensitive devices (computer, mobile phone) can be on a Main network, IoT devices on the IoT network; Guest is optional (for any visitors asking to connect). IoT devices include TV streaming devices, home assistant speakers, security cameras, sensors, controllable lights, switches and appliances. They each represent a potential ingress point to the network which they are on. Segregation and isolation reduces the threat surface (paths of attack) to your most sensitive devices. Be aware of changes in your network performance and investigate appropriately. Separating and limiting the number of WiFi devices on either 2.4 GHz / 5 GHz or Main / IoT / Guest can be helpful for both security and WiFi performance. For example, a streaming service (SmartTV or streaming device) could connect to your 5 GHz IoT network while all the rest of your IoT devices (i.e., security cameras) connect to your 2.4 GHz IoT network and your computer and mobile phone connect to your Main (2.4 GHz and 5 GHz) networks.
Device purchases: The Manufacturer and supported functions matter. For example, WPA3 (the current recommended encryption algorithm) is supported in WiFi 6 and later (including WiFi 6e, 7, and 8 devices). Buying a WiFi 6 Mesh Network may provide a current encryption algorithm at a lower price, but it is likely the device will not receive future manufacturer security updates as often or as long as devices supporting a more current standard such as WiFi 7.
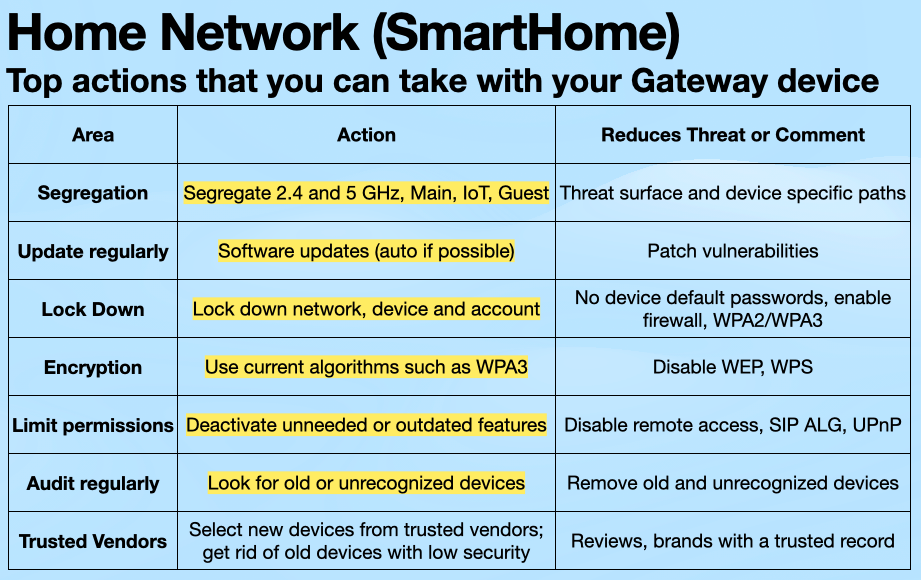
2. Home Networks and Gateway Configurations
Gateways (Routers, Cable Modems, Mesh) Advice: Segregate networks (Main, IoT, Guest). Replace outdated devices that do not receive vulnerability updates from the manufacturer because of age. Update firmware (auto) and reset the device weekly (often can be scheduled), change default password, enable the firewall and current algorithms (use WPA2/WPA3, disable WEP, WPS), periodically check the list of connected devices and offline clients, disable remote management and outdated protocols, isolate devices (limit cross device communications), disable SIP ALG and UPNP port forwarding.
Applications Advice: Be very picky about what you install. Stick to the recognized application stores (Apple’s App Store for iOS and macOS, Google’s Play Store and/or Amazon’s Appstore for Android, Microsoft Store for Windows), but also check reviews and ratings before downloading - a recognized store does not guarantee an application is safe. For specific software (like Adobe, Microsoft Office, etc.), downloading directly from the developer’s website is likely the safest option - always check the url carefully. Update the Apps that you use as these often include security updates. Disable and Remove Apps that you no longer use.
Device hardware should receive security updates to close new vulnerabilities as they are discovered - if they are no longer supported by the manufacturer, it may be time to replace them. For example, Android phones support (security updates) may be as little as 3 years or as many as 7 years.
Using a Password Manager helps you use Passkeys (preferred) or Unique Passwords on your accounts. Creating your own passwords is not recommended due to both credential stuffing and brute force attacks. Passkeys (which are tied to specific device) are more secure than passwords.
Consider an Authenticator Application: Authenticator hardware (FOB) or authenticator apps are stronger than a texted code to your phone since your phone could be compromised via a SIM card Swap.
Use Privacy and Security Settings (on devices/operating systems and within browsers or applications; review them for use periodically - for example, OS functions such as Apple’s Private Relay.), Limit Sharing on Social Media (the less the better). Browsers should leverage security and privacy settings available including items such as hiding IP address, and preventing cross-site tracking. Location Services should be set to Never unless functionally necessary or desired (for example, a Map application or Camera which can be set to active only when using the application). Always restrict application permissions to the greatest reasonable extent.
Anti-virus and VPN: Bucks County Home Networks acknowledges the value of additional anti-virus software and VPNs - more protection is better protection, but also aims for enough protection based on individual behaviors. Noting that operating systems (Windows, macOS, iOS, Android) all include anti-virus and privacy functions, not having an explicit 3rd party anti-virus or VPN service does not leave an individual unprotected; however, insure that the OS is properly configured for your needs (for example, enabling Private Relay in macOS and iOS although the configuration requires using Safari). If you want the extra protection afforded by 3rd party software, do your homework. Realize too that some VPN services include an anti-virus function that examines downloads before it ever gets to your device (an example is NordVPN).
Phishing (pronounced “fishing”) and Scams: come in many forms and may look like something from someone you know - email and text messages with links or attachments, phone calls, messages indicating you won a prize or an undeliverable package or order confirmation, messages asking for any kind of personal information, fake websites, fake ads, surveys, on-line quizzes, and even links within legitimate websites that have been compromised. Just because something looks like it came from a friend or family member does not mean that it actually did - and even if it did come from someone you know or trust does not mean that it is safe.
Do NOT click the link and Do NOT provide requested information unless you are certain that you initiated the contact directly with the organization requesting the information. SLOW DOWN and TRUST SLOWLY when navigating online.
More information on phishing is available from the National Institute of Standards Technology (NIST), a group within the US Department of Commerce (again, right click to copy the link, paste it into your browser address bar and verify):
https://csrc.nist.gov/projects/human-centered-cybersecurity/research-areas/phishing
Caution Summary: Assume your private information is already available to bad actors, but protect your information anyway. Strong passwords and strong authentication are important safeguards. Be aware of third-party apps, impersonation attempts, and ensure software is up to date. Be skeptical of unsolicited messages and links, especially from unknown accounts. Be aware of common warning signs that your information is actively being exploited such as Account access problems, Notifications of unexpected transactions or activity - may indicate a stolen credit card, or Problems sending texts - may indicate stolen phone number (also called a SIM card Swap).
Zero Trust, Least Privilege and Defense in Depth should be reflected in both your mindset and your device configurations.
3. Computers and Mobile Phones and Other Devices
Safeguard Against Eavesdropping by restricting microphone or camera use, and limit location sharing. Schedule Device Reboots to help remove potential malware. Turn off bluetooth if it is not needed (especially on mobile device). Disable WiFi on any device that doesn’t need it. Avoid public WiFi, including hotels, public venues (stadiums) and coffee shops - do not connect automatically; Cellular is more secure than public WiFi. Exercise Secure User Habits - back up data, use secure storage methods, and enable account recovery options. Enable Full Disk Encryption to make disks unreadable to an attacker and Create Restore Points in case of compromise.
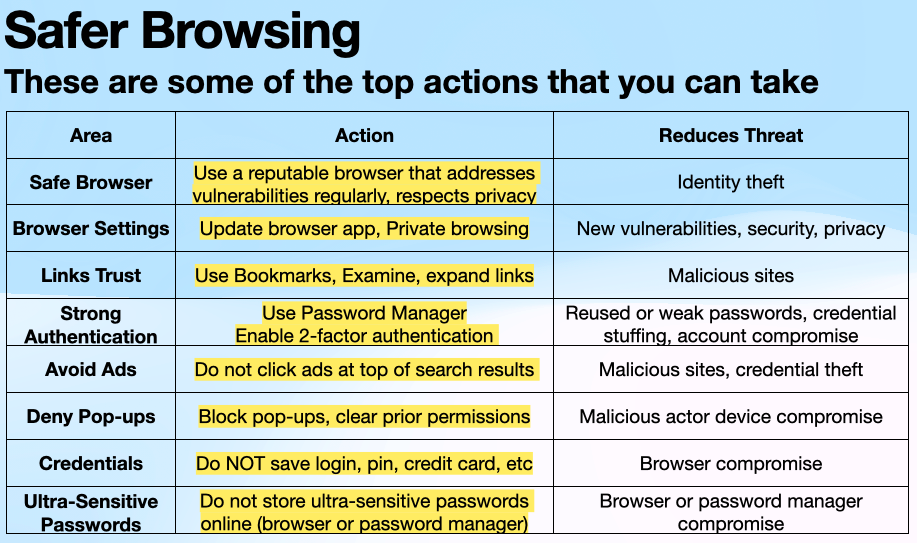
Browsing the Web and Web Based Applications Advice: Do NOT click any link or open any file that you are not sure about. Use a Modern Browser and keep it updated for better security. When browsing on the internet, verify the address bar has a “lock” or begins with https:// indicating a secure connection as well as the actual address you want to reach. Using Bookmarks for often used accounts is recommended, but still verify the domain (part of the url right before the .com or .org).
Consider switching to a browser such as Brave, which is “privacy by default,” blocking ads and trackers, and also changing the search engine to DuckDuckGo, which is also “privacy by default” with a better user experience. Use a Password Manager and opt for Passkeys if the application supports them. Use Encryption. Attackers may mimic a real site in the hope that an unwary user will download malware - this specifically includes the Ads that typically come through at the top of a search result (avoid all Ads at the top of a search). Use the privacy settings in a browser to limit tracking.
Computers and Mobile Devices Advice:
Shut down computer when not in use. Upgrade Operating Systems Automatically for the latest security updates, Employ Security Software - enable firewall, use antivirus and anti-malware software (computer and mobile phone OS typically include antivirus and anti-malware software - there are also fee-based 3rd party software that can be used), Protect Passwords by using a password manager to keep passkeys and/or passwords complex and unique. Use Multi-factor Authentication and current Encryption algorithms.
4. Personal Accounts (Email and Phone)
Email Advice: Do not open ANY unsolicited or unexpected attachments or links - this includes that link that your friend sent you. Do not share personal or financial information via email as companies do not (and should never) ask for it through e-mail; always contact the company directly via known contact paths such as a bookmark of a verified secured url. Consider having one primary email address for sensitive accounts and do not use this on other accounts (such as social media). Verify your email client uses TLS (Secure IMAP or Secure POP3). Protect email access with a strong password with 2FA noting that a passkey or an authenticator app is better than text verification (SMS). Check sender email addresses being cautious about spoofed addresses and suspicious senders.
Text Messaging Advice: Do not open or click ANY link in text messaging. Do not send sensitive information via text without an end to end encryption application such as Signal.
Phone Advice: Lock down your account changes with your carrier (methods may vary by carrier). Do NOT answer calls from unrecognized numbers (a legitimate caller will leave a message - be skeptical and trust slowly).
NOTES: Financial institutions, health insurance and other account verifications may use email or text messaging to verify a user login. Email accounts may be taken over and Text messages can be intercepted (it is much better than nothing, but a 2FA application or token is better). SMS, MMS and RCS Text messaging does not have end to end encryption support (your cellular carrier can see your messages and protocol weaknesses may allow others to see them too). Messaging on Android and iOS can be encrypted end to end with special purpose applications such as Signal and WhatsApp (a Meta owned application). Comparing the two applications on privacy and security, Signal application is recommended for its superior transparency and privacy policies. Both sender and receiver have to have the same application to communicate.
Phone Number: Be aware that a scammer may target your cellular carrier to steal your phone number (SIM swap) after which the scammer may attempt to impersonate you and would be able to use 2 factor authentication (by receiving the texted code on your phone number) to potentially login to you financial accounts.
Social Media Advice: For privacy and security, set your account to private and limit what you share on social media (for example avoid posting personal information, limit information you do post to friends only, opt-out of sharing to search engines). Be cautious about sharing personal information, including photos or vacation plans. Review and adjust privacy settings regularly, and use a password manager with two-factor authentication to protect your accounts. Monitor your account activity and restrict location sharing.
Handling Misinformation and Disinformation Advice: When you encounter misinformation (inadvertently misleading content) or disinformation (intentionally false content), AVOID ANY direct engagement. Do not reply, comment negatively, or react with emojis, as these actions increase the post’s visibility and spread. If you feel you absolutely need to do something, contact the person who posted it via another channel and ask them to take it down, or report it to the platform if it violates their policies. Engaging with the post, whether positively or negatively, will help it spread further due to the platform’s algorithm, which prioritizes engagement.
Trustworthy News and Reliable Information: Nobody enjoys being deceived, yet choosing reliable, credible, and trustworthy news sources can be difficult. “News” pours in from everywhere, but much of it is NOT News at all - including entertainment media, clickbait and fake news websites, social media posts and memes, echo chambers and bubbles, outlets with unknown or vague ownership, tabloids, podcasters, influencers and bloggers without credible sources, propaganda, and biased news aggregators …all of which are unfortunately also much easier to manipulate than the traditional rigorous reporting that were the main sources for current information decades ago. We aim to distinguish between news and entertainment, acknowledge that facts are objective rather than a reflection of personal identity, and recognize that most people share a common reality, even if their perspectives differ.
Misinformation is inadvertently misleading content while Disinformation is intentionally false content (actual lies). Bias is a slant favoring one perspective over another. The intent of specifically configuring News sources is to minimize Misinformation, Disinformation and Bias before you spend your valuable time on it. Please see the About page for why Bucks County Home Networks feels qualified to help in this area with optional free news source configuration.
News: Quality news—whether in print or online—requires significant resources to produce, and the business model for news organizations is often difficult. Subscribing to local newspapers like the Bucks County Courier Times, Bucks County Herald, or Philadelphia Inquirer directly supports local journalism. Subscriptions to major outlets like Reuters, The New York Times, The Wall Street Journal, or The Washington Post help sustain free journalism on a larger scale. All of these sources contain both News and Opinion which are most often labeled as such.
There are free news aggregators...Services such as Apple News, BBC News, Google News, and Microsoft News provide stories directly to your mobile phone or computer, often with customizable topics to better fit your interests noting that your specific media selections may impact the quality of the feed.
Fact-checking and bias verification: To evaluate a source’s credibility, check its reputation, track record, author credentials, and primary sources. Look for independent confirmation from other trustworthy outlets. Be mindful of context, timelines, and the difference between opinion and objective fact. Fact-checking websites such as FactCheck.org, Reuters Fact Check, The Poynter Institute, and PolitiFact are excellent resources. Bias evaluations have been credibly performed by websites such as MediaBiasFactCheck, AllSides and adfontesmedia.
Be Wary of Sensationalism: Avoid sensational headlines or clickbait. These often mislead or exaggerate for attention. If something seems too good or too awful to be true, it’s worth double-checking before believing or sharing it. Platforms like Facebook, X (formerly Twitter), BlueSky, Mastodon, TikTok, and Instagram should not be relied on for accurate news (of these platforms, BlueSky appears to be best on user privacy and has committed to not train generative AI tools with user data). These platforms are not verified sources, and information found on them is often unreliable. In any case, the less you share about yourself, the better for your privacy and security.